Know About Access Card Duplicate Singapore
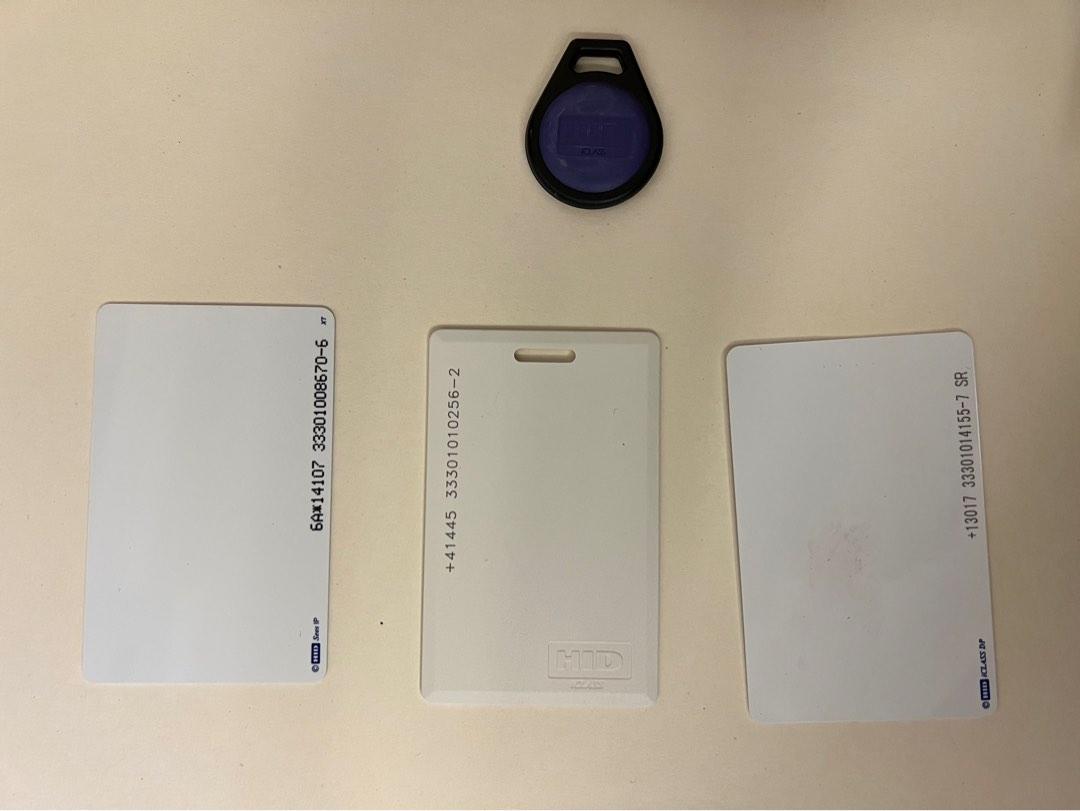
Because of the security given by access card duplicate singapore, businesses of any size are focuses on of assault. The organization is in serious jeopardy today if any worker utilizes a badge or important fob to get not authorized access to the constructing or How to identify access card using smartphone Singapore any one of the building’s areas.
A business using duplicate charge cards to get in the property should continue carefully. Far more attacks objective credit cards that utilize technology too old to take care of contemporary improvements. A business might take several steps to increase stability and make it more challenging for unauthorized people to go into. Don’t let them seize what is your own, while keeping your wits of you.
Multi-Aspect Or Two-Element Authorization Accessibility Control Process
One way to protect against men and women while using bogus cards is usually to mandate multiple-element authentication. Personnel may get entry within a multiple-step method applying this way.
Staff members with gain access to greeting cards nevertheless the admittance also must create yet another kind of recognition for the reason that doorway or area has a protected access control method. Typically, a private detection amount (PIN) must be put into a keypad which is either near by or connected to the system involved. Most cards viewers merge a keyboard and visitor in to a single product.
Video camera Community Entry Handle Program
In addition, some institutions may deploy surveillance digital cameras to observe for distrustful behavior or gather proof a bogus ID to get entry.
Several video clip managing and entry management solutions give cross-program contacts to streamline this process. If this type of strategy identifies a breach, it could use the finished video data to fix the problem with duplicate iclass card singapore.
Biometric Identifying And Entry Management System
Using biometric authorization strategies remains another choice. This method is proper and ideal for safeguarding a business’s entry manage process. The most prevalent form of biometric authorization is a person’s fingerprints.